A Japanese Floodgate. Y2K. And Why Los Angeles Businesses Keep Skipping the Most Important IT Investment
THE SHORT ANSWER
A Japanese mayor spent decades being mocked for building a massive floodgate his village did not want. When the 2011 tsunami destroyed the entire coastline, his village was virtually untouched. Zero deaths behind the gate. Y2K is the same IT security prevention story in a different building. Governments and businesses worldwide spent an estimated $300 to $600 billion preparing for the year 2000 date rollover bug. Both share one lesson: prevention is invisible when it works, and invisibility gets mistaken for evidence that it was never necessary. That mistake is exactly how businesses end up skipping IT security prevention in Los Angeles until the wave arrives and paying far more than the cost of the floodgate they refused to build.
IT Accuracy | Managed IT Services, Los Angeles | Date: April, 28 2026 | 9 min read

AT A GLANCE
✓ Prevention that works produces no headlines and no crisis
✓ Wamura’s floodgate cost less than the tsunami damage it prevented
✗ Y2K was not a hoax — it was prevention that worked too well to be believed
! Businesses that skip the floodgate pay far more when the wave arrives
! The average US data breach cost $10.22 million in 2025
✓ IT Accuracy finds your vulnerabilities before a threat actor does
IT security prevention in Los Angeles has a specific frustration built into it: nobody throws you a party when nothing goes wrong. Nobody writes a headline that says nothing bad happened today. Prevention is invisible by design, and that invisibility is exactly why so many businesses skip it until it is too late.
The Mayor Nobody Wanted to Listen To
Kotoku Wamura was the mayor of Fudai, a small fishing village in northeastern Japan. He had lived through two devastating tsunamis, one in 1896 and one in 1933, that together killed 439 of his neighbors. He watched bodies being pulled from the earth. He made a decision that any IT security prevention professional in Los Angeles would recognize: document the threat, build the control, and never let it happen again on his watch.
So he built a floodgate. A massive one. Fifteen and a half meters tall, spanning 205 meters across the mouth of the Fudai River. Construction took twelve years and cost 3.56 billion yen, about $15 million USD at the time of completion in 1984, or roughly $46 million in 2026 dollars. The town council pushed back hard. Residents complained. Critics called it a monument to one man’s paranoia and a grotesque waste of public money.
At his retirement ceremony he told village employees: “Even if you encounter opposition, have conviction and finish what you start.” It is the same thing IT security prevention requires — sustained commitment before anyone can prove it was necessary.

By Sed — Own work, CC BY-SA 3.0, via Wikimedia Commons
On March 11, 2011, a 9.0 magnitude earthquake triggered a tsunami that hit Japan’s northeastern coastline with 66-foot waves. Entire towns were erased. Nearly 20,000 people died. The coastline looked like a war zone.
In Fudai, workers remotely closed the floodgate’s panels. One firefighter had to rush down and shut a jammed panel by hand as the water came. The tsunami hit. Water crested the top of the gate. And behind it, the village was virtually untouched.
After the tsunami, residents made the trip to Wamura’s grave to pay their respects to the man they had spent years mocking.
It cost a lot of money. But without it, Fudai would have disappeared.
Satoshi Kaneko, Fudai fisherman, speaking to NBC News after the 2011 tsunami
What the Floodgate and Y2K Teach Us About IT Security Prevention
The story of Wamura’s floodgate circulates every few years because the lesson it carries is so clean and so uncomfortable. People resent the cost of prevention. They will scrutinize a budget line for a security measure they have never needed and never think about if it works. Then when something goes wrong, the first question is always why nothing was done to prevent it. The answer almost always traces back to skipped penetration testing — a penetration test that never happened or a security program that got cut in the last budget cycle.
Y2K is the same story in a different building. Governments and businesses worldwide spent an estimated $300 to $600 billion preparing for the year 2000 date rollover bug. When January 1, 2000 arrived without incident, a significant portion of the public decided the whole thing had been a manufactured crisis. The correct conclusion was the opposite. The work had been done so thoroughly that there was nothing left to fail. The silence was the proof, and nobody recognized it as proof because silence never makes the news.
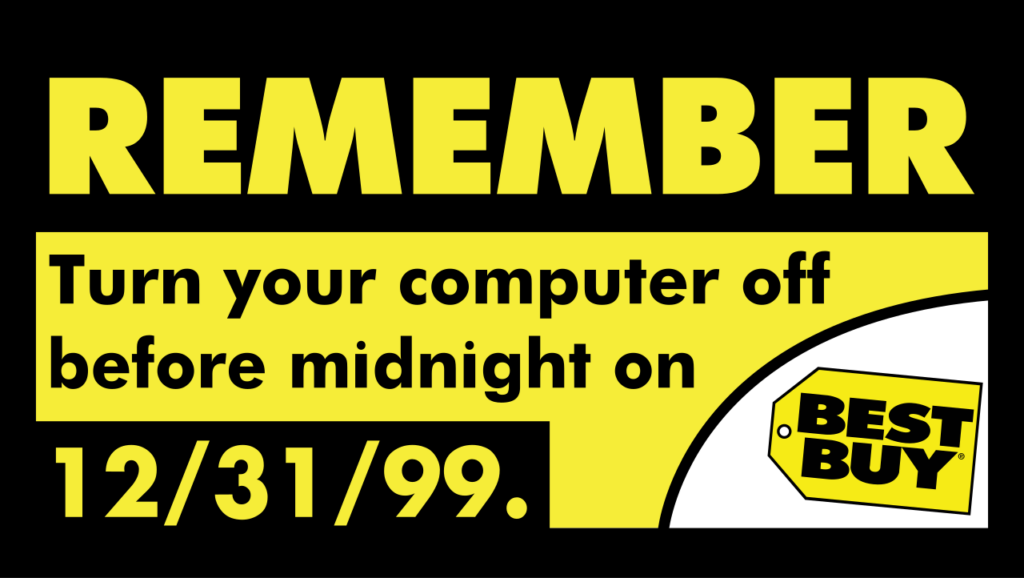
Original: Best Buy. Vector: DraftSaturn15 — Public Domain, via Wikimedia Commons
That is the trap prevention always sets for itself. It works invisibly. And invisibility gets mistaken for evidence that it was never necessary. The budget that funded it becomes the first target when someone decides to cut costs. Which creates exactly the conditions that a proper IT security prevention program in Los Angeles was designed to stop before they become irreversible.
THE PATTERN
Effective prevention produces silence. Silence gets mistaken for evidence that the threat was never real. That mistake leads to cutting the budget. Which creates the conditions for the thing that was being prevented. This is not hypothetical. It is the documented lifecycle of security investment in organizations of every size.
Does your business have a floodgate?
IT Accuracy can assess your current infrastructure, identify every vulnerability in your attack surface, and build the security program that keeps the wave from ever reaching your business.
The IT Security Prevention Cost Comparison
The IT security prevention lesson in the floodgate numbers is simple. The gate cost 3.56 billion yen — about $15 million USD when completed in 1984, or roughly $46 million in 2026 dollars. The fishing port losses from the tsunami alone came to 3.8 billion yen in a single afternoon.
The IT security prevention investment cost less than the damage it prevented. And that calculation does not include a single human life.
THE NUMBERS
Floodgate cost
¥3.56 billion
$15M USD in 1984 / ~$46M in 2026 dollars
Port losses from tsunami
¥3.8 billion
In a single afternoon
Deaths behind the gate
Zero
Not counted in any financial comparison
What IT Security Prevention Looks Like in Your Business
IT security prevention works like the floodgate — it costs money every year whether the wave comes or not. Cybersecurity works the same way. You pay for monitoring that catches intrusion attempts you never hear about. You pay for patch management that closes vulnerabilities before anyone exploits them. You pay for penetration testing that finds the weaknesses in your system before a threat actor does.
None of that produces a visible result. The result of good security is that nothing happens, and nothing happening looks exactly like nothing happening. That is very easy to mistake for evidence that the security was never necessary in the first place.
Then something happens. A ransomware attack locks your systems on a Friday afternoon. A phishing email hands over credentials for your entire client list. A misdirected file sends a contract to a competitor. For small and mid-size businesses in Los Angeles, recovery from any one of those events is expensive, disruptive, and increasingly unlikely to be fully covered by insurance without documented security controls already in place. According to IBM’s 2025 Cost of a Data Breach Report, the average US data breach cost $10.22 million. The answer for why businesses get there is almost always the same: IT security prevention — vulnerability assessments, ongoing monitoring, penetration testing — was the line item that got cut.
The Grave Visit Problem
The detail of the Wamura story that stays with you is the residents visiting his grave after the tsunami. Prevention never gets that acknowledgment. There is no grave to visit after a breach. There is only a ransom note, a forensics bill, and a conversation with your legal team.
The better version of the story is the one where you build the floodgate before you need it. Where you do the penetration test that finds the vulnerability before someone else does. Where you have the incident response plan ready before the incident arrives. Where the thing that does not happen is the thing that would have cost you everything.
That is not a dramatic story. It has no villain, no crisis, no resolution. It is just a business that kept running because someone invested in IT security prevention in Los Angeles before the wave arrived. IT Accuracy is the floodgate. The question is whether you want to build it before or after the wave.
HOW IT ACCURACY BUILDS YOUR FLOODGATE
Find the vulnerabilities in your system before someone else does
Most small and mid-size businesses have no IT security prevention program. They have no idea what their actual attack surface looks like and assume their systems are secure until they find out otherwise. IT Accuracy’s cybersecurity and penetration testing services are designed to show you exactly where you are exposed before a threat actor gets there first.
We conduct thorough network audits, identify vulnerabilities across your infrastructure, test your defenses against real attack scenarios, and give you a prioritized action plan. Then we help you close the gaps by building the floodgate before the wave arrives.
- Comprehensive network vulnerability assessment
- Penetration testing that mimics real attack methods
- Prioritized remediation roadmap, not just a list of problems
- Ongoing monitoring so new vulnerabilities do not go undetected
- Incident response planning before you need it
- Clear reporting that non-technical leadership can act on
NETWORK SECURITY TOPIC CLUSTER
IT Accuracy
Managed IT Services — Los Angeles, CA
IT Accuracy provides cybersecurity and security awareness training, managed network services, cloud solutions, and help desk support for businesses across Los Angeles and nationwide.